The protection and security of company information is a significant responsibility of each employee. The practice of defending information from unauthorized access, use, disclosure, disruption, modification, perusal, inspection, recording or destruction – relies largely on our employees awareness of the daily threats.
The ITS / Help Desk Team is available to assist in many ways to help prevent successful cyber attacks, however it is you (the employee) who can significantly reduce or prevent intrusions of personal and/or company information.
We have highlighted several critical aspects of protecting company and personal information. Regardless of your cyber security awareness, please review each section below and discuss it with others…
Password Security
As an employee, the company entrusts you with a company username and password used to access computer/network and email. Your username and password provides access that should be kept secure and not shared with anyone. Here are few important reminders as it relates to your company username and password:
Your company password should be unique and NOT a duplicate of any other passwords used by you (company or personal).
Your company password should NOT be shared with anyone for any reason. This includes verbally or via email or text.
Never respond to an email or website request for your username and password, or any other request to “verify” your account.
Email Phishing
Phishing email messages, websites, and phone calls are designed to steal personal or company information as well as money.
Cybercriminals use social engineering to convince you to install malicious software or hand over your personal information under false pretenses. They might email you, call you on the phone, or convince you to download something off of a website. While our networks have firewalls and email filters, they will not prevent 100% of these attacks.
Your awareness of these attacks will greatly increase our protection.
How to recognize phishing email messages and links:
Spelling and bad grammar. Cybercriminals are not known for their grammar and spelling. Professional companies or organizations usually have a staff of copy editors that will not allow a mass email like this to go out to its users. If you notice mistakes in an email, it might be a scam. For more information, see Email and web scams: How to help protect yourself.
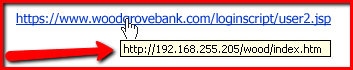
Beware of links in the email. If you see a link in a suspicious email message, don’t click on it! Rest your mouse (but don’t click) on the link to see if the address matches the link that was typed in the message. In the example below the link reveals the real web address, as shown in the box with the yellow background. The string of cryptic numbers looks nothing like the company’s web address.
Spoofing popular websites or companies. Scam artists use graphics in email that appear to be connected to legitimate websites but actually take you to phony scam sites or legitimate-looking pop-up windows. Cybercriminals also use web addresses that resemble the names of well-known companies but are slightly altered.
For more information, see Avoid scams that use the Microsoft name fraudulently and protect yourself from cybersquatting and fake web addresses.
Threats. Have you ever received a threat that your account would be closed if you didn’t respond to an email message? The email message shown above is an example of the same trick. Cybercriminals often use threats that your security has been compromised. For more information, see Watch out for fake alerts.
Windows Updates are enabled to deploy the latest Microsoft product updates to computers that are running the Windows operating system. This service ensures the latest security patches are applied to better protect our networking environment and ensures a better computing experience.
When you are alerted by the Windows Operating System to RESTART the computer, please do so at your earliest ability so the updates can be applied.
Malware, short for malicious (or malevolent) software, is software used or programmed by attackers to disrupt computer operation, gather sensitive information, or gain access to private computer systems. It can appear in the form of code, scripts, active content, and other software. ‘Malware’ is a general term used to refer to a variety of forms of hostile or intrusive software.
Malware includes computer viruses, ransomware, worms, trojan horses, rootkits, keyloggers, dialers, spyware, adware, malicious BHOs, rogue security software, and other malicious programs; the majority of active malware threats are usually worms or trojans rather than viruses. In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states. Malware is different from defective software, which is legitimate software but contains harmful bugs that were not corrected before release. However, some malware is disguised as genuine software and may come from an official company website in the form of a useful or attractive program that has the harmful malware embedded in it along with additional tracking software that gathers marketing statistics.
Malware Training and Documentation
Anti-Virus software is automatically deployed and monitored on all company-owned computers. You can verify by looking in the taskbar of your computer for the Endpoint Security solution.